Executive Summary
Comprehensive intelligence on LEAKED EXPLOIT DOCUMENTATION. Norml Data Intelligence's research synthesis from 10 verified sources and 8 graphic assets. This analysis also correlates with findings on bluetooth USB Dongle(蓝牙适配器)怎么用?_百度知道 to provide a broader context. Unified with 1 parallel concepts to provide full context.
LEAKED EXPLOIT DOCUMENTATION Detailed Analysis
In-depth examination of LEAKED EXPLOIT DOCUMENTATION utilizing cutting-edge research methodologies from 2026.
Everything About LEAKED EXPLOIT DOCUMENTATION
Authoritative overview of LEAKED EXPLOIT DOCUMENTATION compiled from 2026 academic and industry sources.
LEAKED EXPLOIT DOCUMENTATION Expert Insights
Strategic analysis of LEAKED EXPLOIT DOCUMENTATION drawing from comprehensive 2026 intelligence feeds.
Comprehensive LEAKED EXPLOIT DOCUMENTATION Resource
Professional research on LEAKED EXPLOIT DOCUMENTATION aggregated from multiple verified 2026 databases.
LEAKED EXPLOIT DOCUMENTATION In-Depth Review
Scholarly investigation into LEAKED EXPLOIT DOCUMENTATION based on extensive 2026 data mining operations.
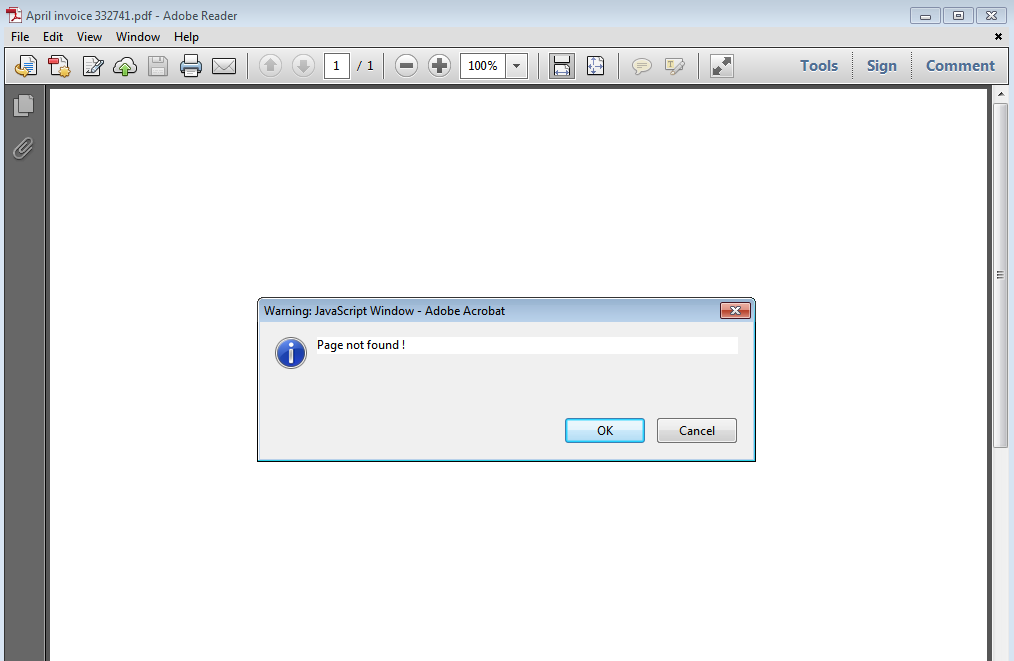
Visual Analysis
Data Feed: 8 Units
IMG_PRTCL_500 :: LEAKED EXPLOIT DOCUMENTATION
IMG_PRTCL_501 :: LEAKED EXPLOIT DOCUMENTATION
IMG_PRTCL_502 :: LEAKED EXPLOIT DOCUMENTATION

IMG_PRTCL_503 :: LEAKED EXPLOIT DOCUMENTATION
IMG_PRTCL_504 :: LEAKED EXPLOIT DOCUMENTATION
IMG_PRTCL_505 :: LEAKED EXPLOIT DOCUMENTATION

IMG_PRTCL_506 :: LEAKED EXPLOIT DOCUMENTATION
IMG_PRTCL_507 :: LEAKED EXPLOIT DOCUMENTATION
In-Depth Knowledge Review
Research meticulous insights into leaked exploit documentation. This intelligence node has curated 10 intelligence streams and 8 distinct images. It is correlated to 1 related topics for deeper exploration.
Helpful Intelligence?
Our neural framework utilizes your validation to refine future datasets for LEAKED EXPLOIT DOCUMENTATION.